Ashish Malik : iforensic.wordpress.com
M.Tech – Information Security & Computer Forensics
Mail : ashishmalik10@gmail.com, ashishmalik10@yahoo.com
==================================================
The use of cyber space for criminal activities has brought the issue of cyber security in the spotlight.
There have been many cases of such activities where malwares like stuxnet, flame, slammer etc. have been used for industrial sabotage and espionage purposes.
Over the past few years, the focus of many researches has been towards various implantable medical devices. Although, no specific attack on such devices has come into view but researchers have been digging into the possibilities of various attacks against various implantable medical devices such as pacemakers, insulin pumps, blood-glucose monitor etc.
These life saving devices have data storage, web connectivity and wireless communication. But, these characteristics leaves the devices susceptible to attacks. Since, implantable medical devices can now communicate wirelessly, it makes them vulnerable to hacking attacks. The main problem with these devices is that they can’t be updated without being recalled, unlike computers or mobile phones which get security at regular intervals.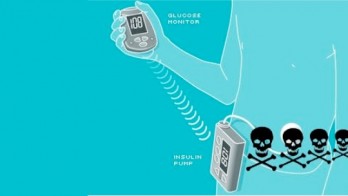
These medical devices have some kind of computer code embedded in them which might be inserted in a patients body. Without such softwares in medical devices, many medical treatments could not exist and implants do help patients lead a normal and healthy life. But software also brings with it inconvenient risks because the software is sure to have bugs.
In a possible attack scenario, privacy of a patient may be compromised which can include determining whether the patient has an implanted device, type of implanted device and serial number of the implanted device etc. The attacker can also identify patient’s name and obtain his history. The most dangerous par is that the hacker can change the device settings, change or disable therapies and deliver a command to the device that may actually threaten the life of the patient. So, there is an actual possibility of not only getting private information about the patient, but also killing the patient. Another attack scenario is to run down the device battery and thereby carry out a power ‘denial of service’ attack. Other types of attacks like insecure software updates or buffer overflow attacks can also be exploited by the hackers if the software code running on the implanted device has bugs in it.
Earlier in 2011, a security expert named Jerome Radcliffe hacked his insulin pumps hardware. He demonstrated that insulin pump can be disabled by using a small radio frequency transmitter. He was also able to control the amount of insulin that was being pumped by the insulin pump.
A troubling element of such research is that it could inspire others to pursue these real-world attacks. Each vulnerability that’s discovered raises the possibility that someone bent on destruction will attemp to exploit it in the real world. Scientists are researching ways to prevent tampering with these devices. One such attempt is the use of jamming signals to stop hackers from such lethal attacks. Reseachers have developed a wearable jamming device which blocks all the radio broadcasting “noise” on the implant device frequency. So, it prevents the attackers from recieving the device data.
Researchers believe that individual hackers likely won’t be able to suddenly tamper with these devices anytime soon, but criminals familiar with medical technology could pose a threat if they attack a specific device. It’s time for the authorities to start taking these security risks seriously. Corresponding authorities must check for the medical device security by examining the software code that is running in these devices and eliminating any or all vulnerabilities present. In a perfect world, nobody would ever exploit those vulnerabilities. So, let’s hope that malicious attacks against medical devices remain in the realm of theoretical.